Microsoft News & Guides Provided By Gitbit
Her Story with a little help
I share the journey of helping a close friend bring her unique story to life online. After years of living on the road in her van, she has so much to share—but she needed a little help finding her voice in the blogging world. Together, we’re exploring how her story can connect with others on Pinterest, using AI as a surprising partner to organize and capture her experiences. It’s been a fun, experimental process full of learning, laughter, and the hope that her journey will resonate with others searching for inspiration and adventure.
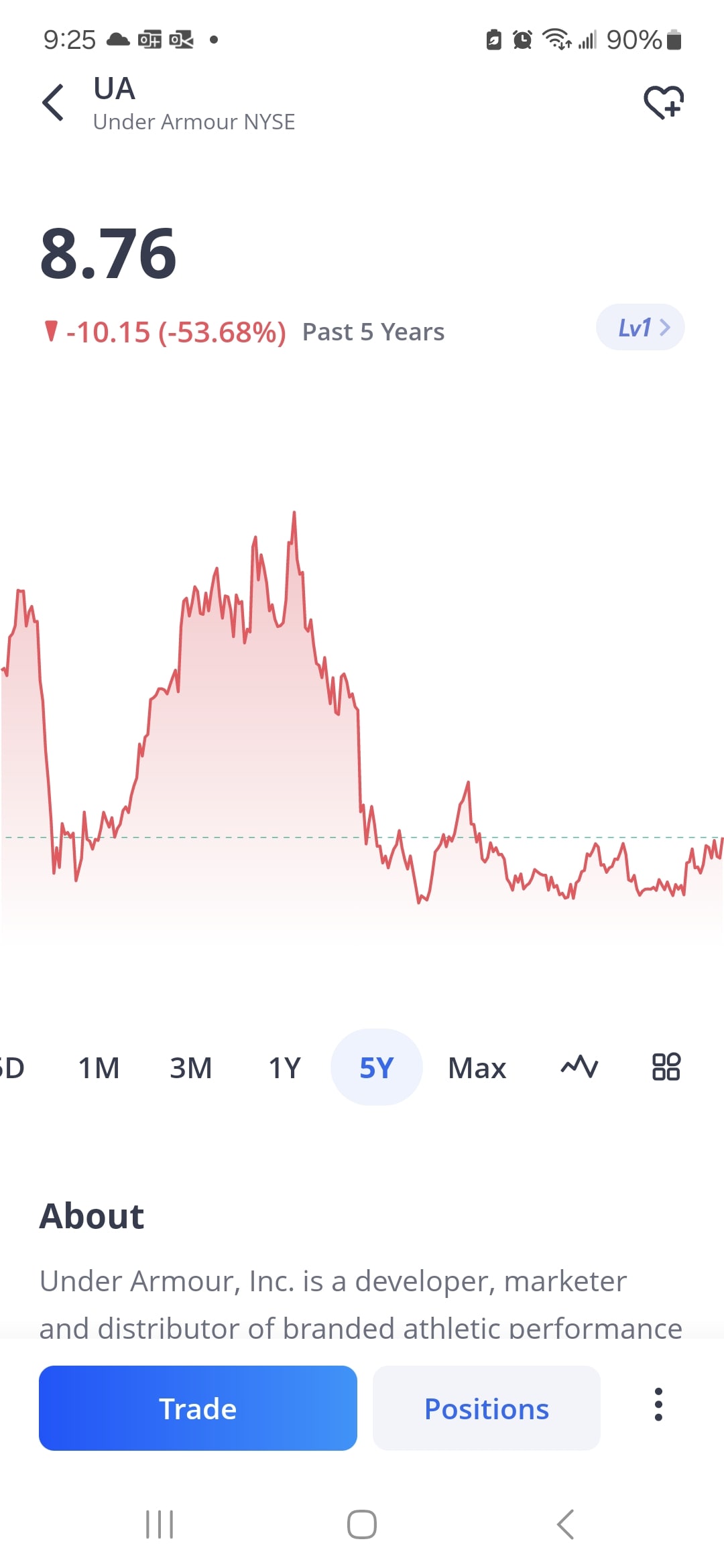
I lost money using AI investing!
I asked Microsoft's AI to pick stocks. I was up 4 days but lost it all and more on one day of trading!

10 Iconic Lyrics That Will Make You Rethink Your Life Choices (You Won't Believe #3!)
You'll be surprised what all ten of these songs are actually about.

I added high-low to my online casino
Adding a new game to my online casino was super easy. It took me 5 minutes and 2 prompts.

I'm not evil but I do have 5 kids.
Whenever I grab food, my kids are like baby birds, hoovering around me squeaking until I give them a bite. But with 5 kids I wouldn't get any part of the food if I gave them all a bite. So, I do what every parent does, I tell them it's hot and they won't like it.
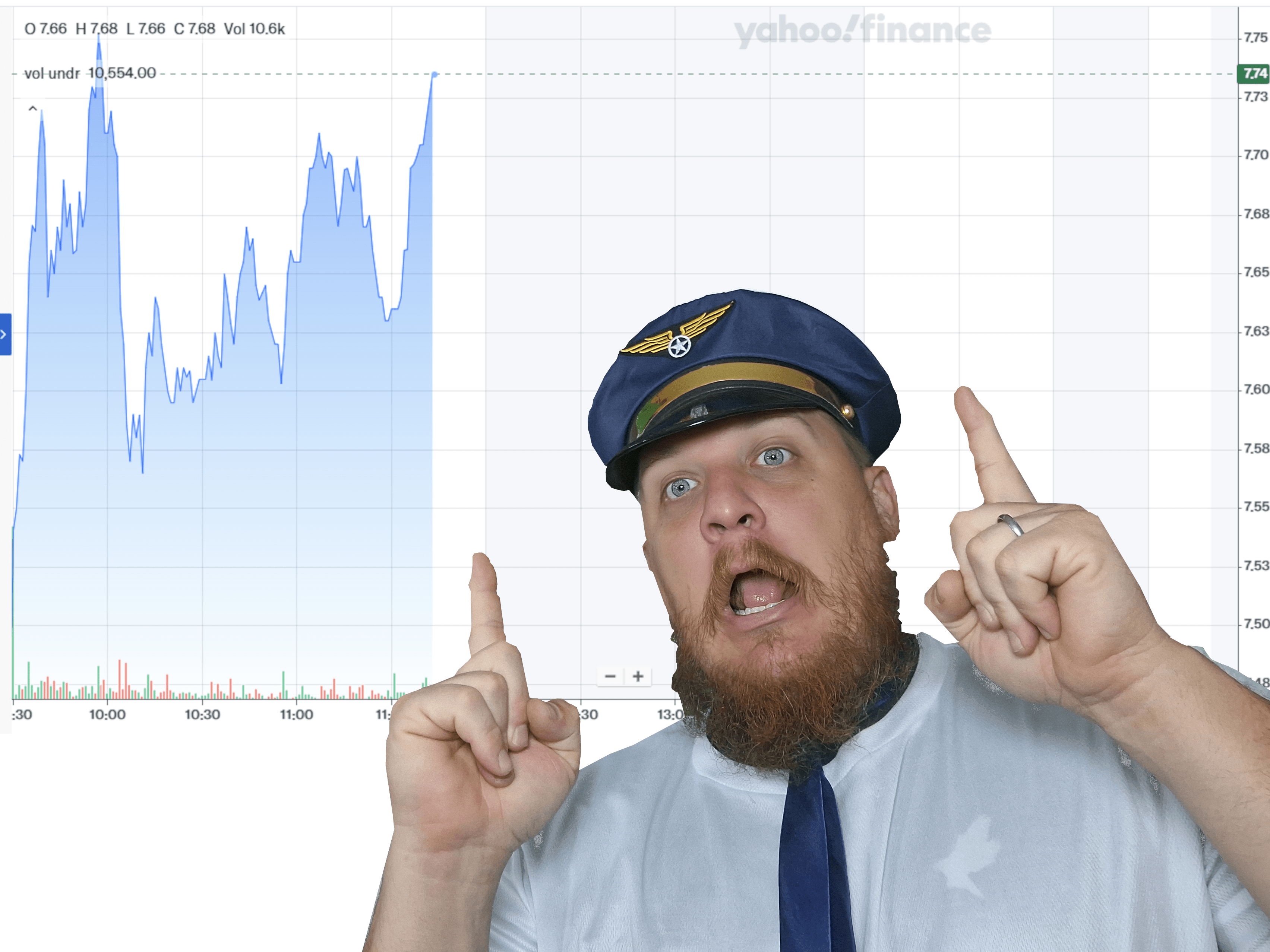
I made 1% day trading with AI!
I made 1% by day trading with AI. It took an entire 15 minutes of my life. Here's how.
I added scratch cards to my online casino!
I created a scratch card game and added it to my online casino. I used AI for the development, and it took a whole 15 minutes to create and publish!

Find the three errors in this AI generated video
Can you find the errors in this AI generated video / image?

one sentence horror stories
50 one sentence horror stories with happy endings

How to get viewers to watch 100% of your Short / TikToks
I asked AI how to get people to watch 100% of my YouTube Shorts. Here's the advice it gave me.

Here's what AI thinks the Phillies need to change for next year
If AI was in charge of the Philadelphia Phillies, what changes would it make?

Hear me out: A dog / toddler saddle
I have an almost 1 year old. She's small. And I have a rescue dog that's pretty big. So, I thought, dog saddle!

I asked AI to create a viral YouTube Short!
Ever want your content to go viral? Here's what AI came up with!

I used AI to create biblical angels
What does AI think a biblical angel would look like?

AI believes the Dodgers will win the world series. Here's Why
AI believes the Dodgers will win the world series. Here's Why
Is AI going to replace Developers?
Is AI going to replace developers? No, but here's 5 ways it can help.

Murder Mystery: ChatGPT vs Copilot
I pit ChatGPT against Microsoft Copilot in a murder mystery!

I broified Copilot
I broified Copilot and the answers were... mildly entertaining. Imagine a millennial pretending to be a bro and answering your questions. That's how Copilot responded.
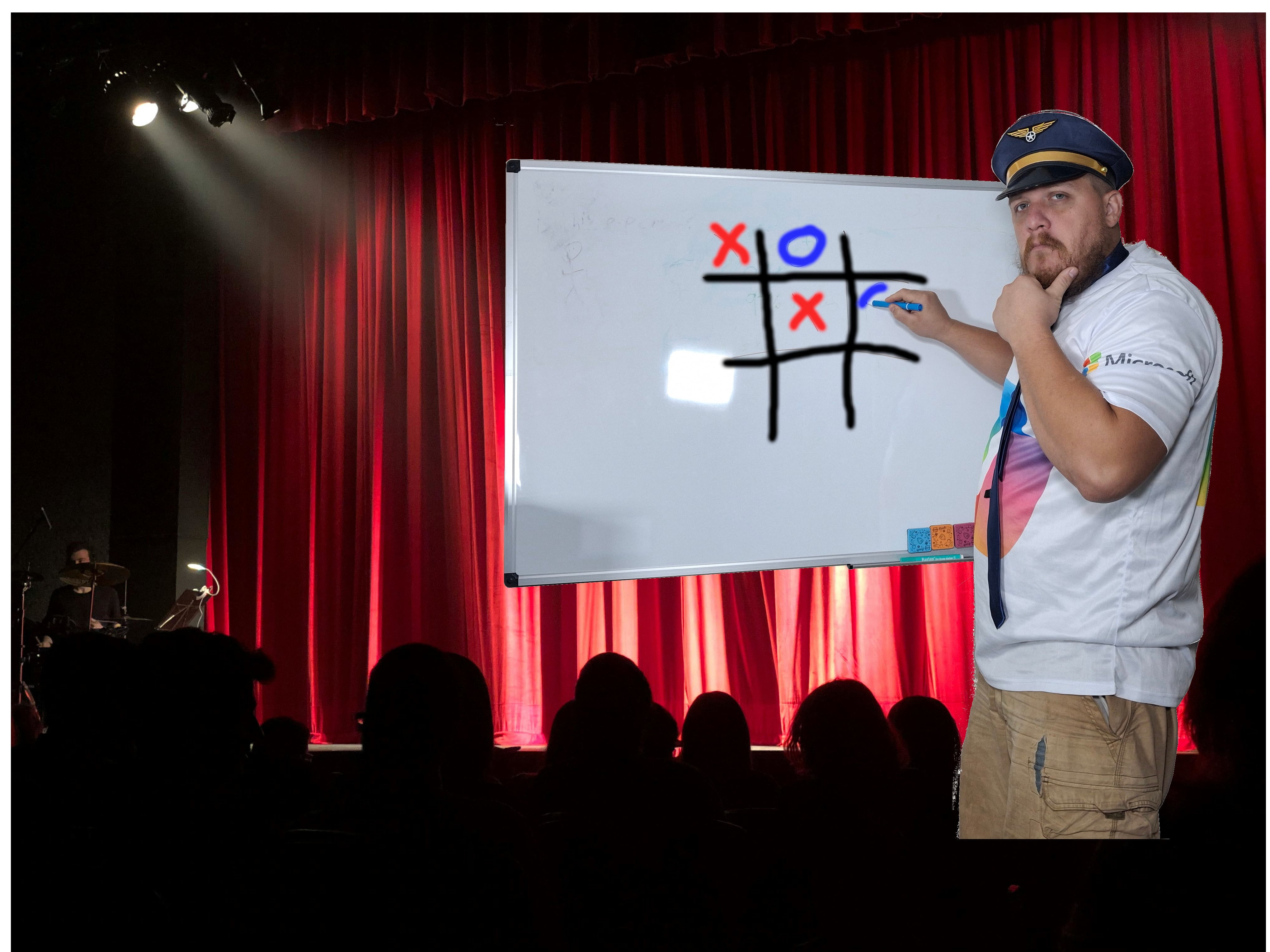
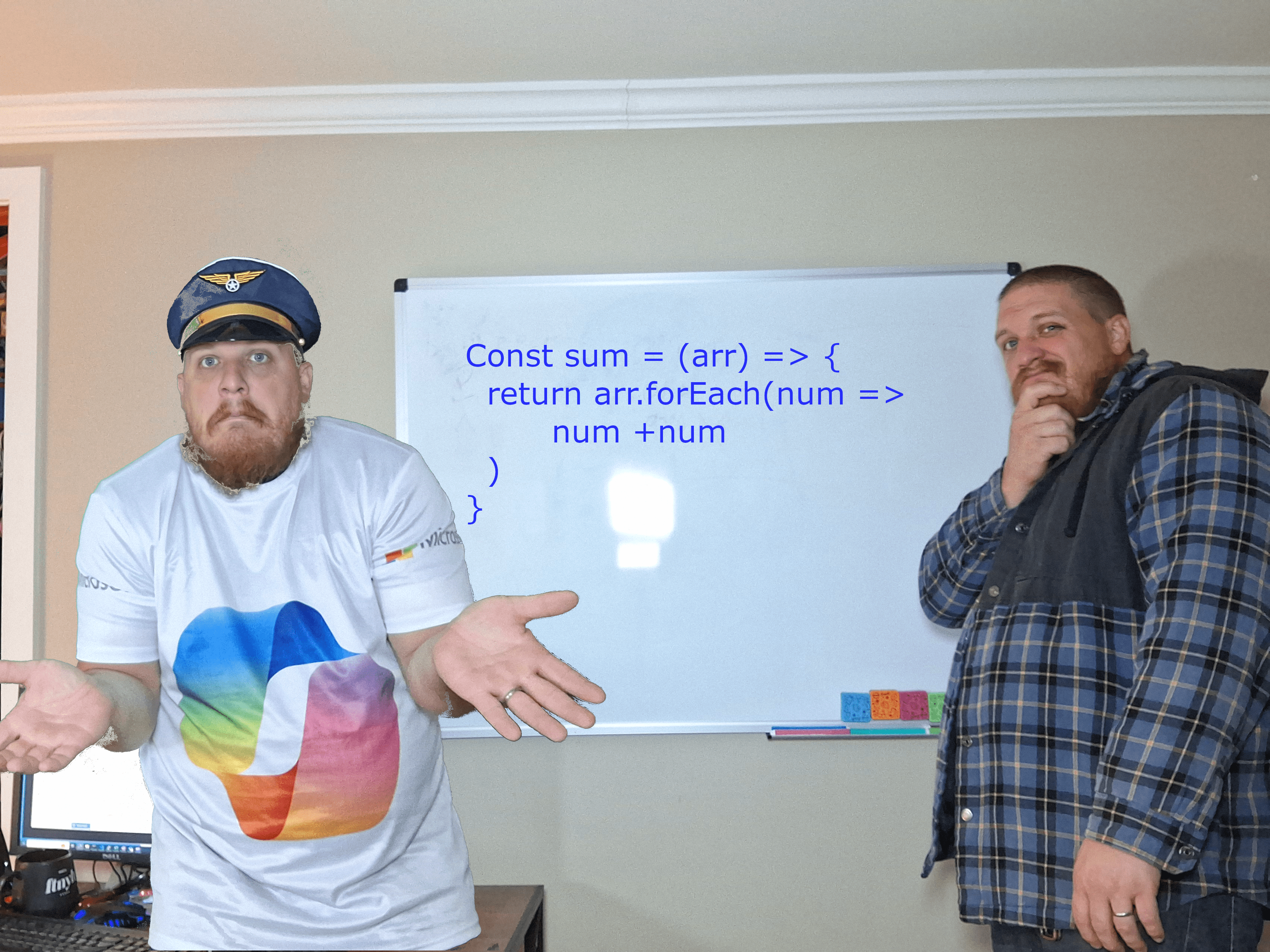
I created a tic-tac-toe game for my online casino using AI!
How I created a web-based tic-tac-toe game using AI. I made some mistakes along that way that I explain and how I would avoid them in the future.
License - What & How Gitbit Allows You To Use Our Content
This document contains the licensing information for GitBit, as well as the Copilot course

Why I chose Copilot over ChatGPT and Gemini. The answer will probably surprise you
The answer to which AI you should use may differ, but my take is probably one you haven't thought of.
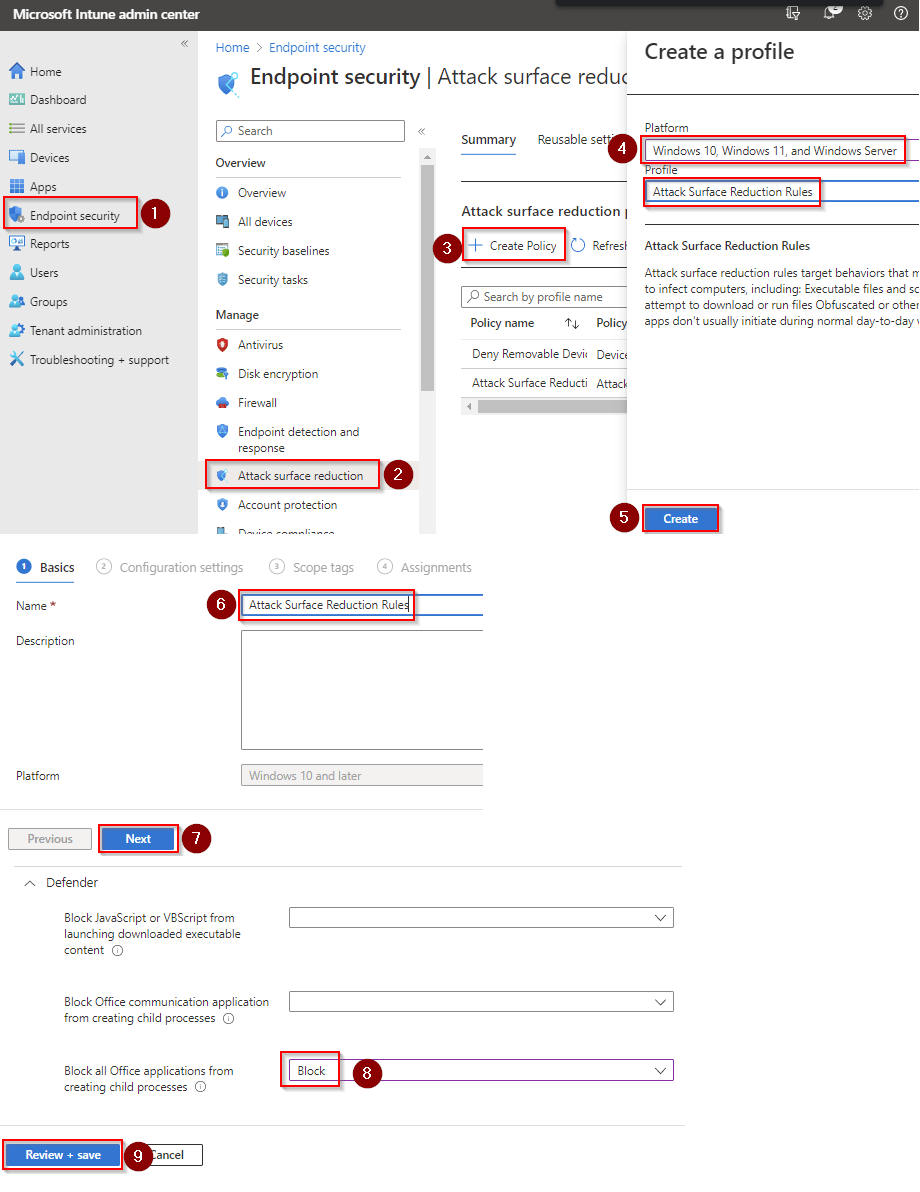
Block Office communication application from creating child processes
How to Block Office communication application from creating child processes
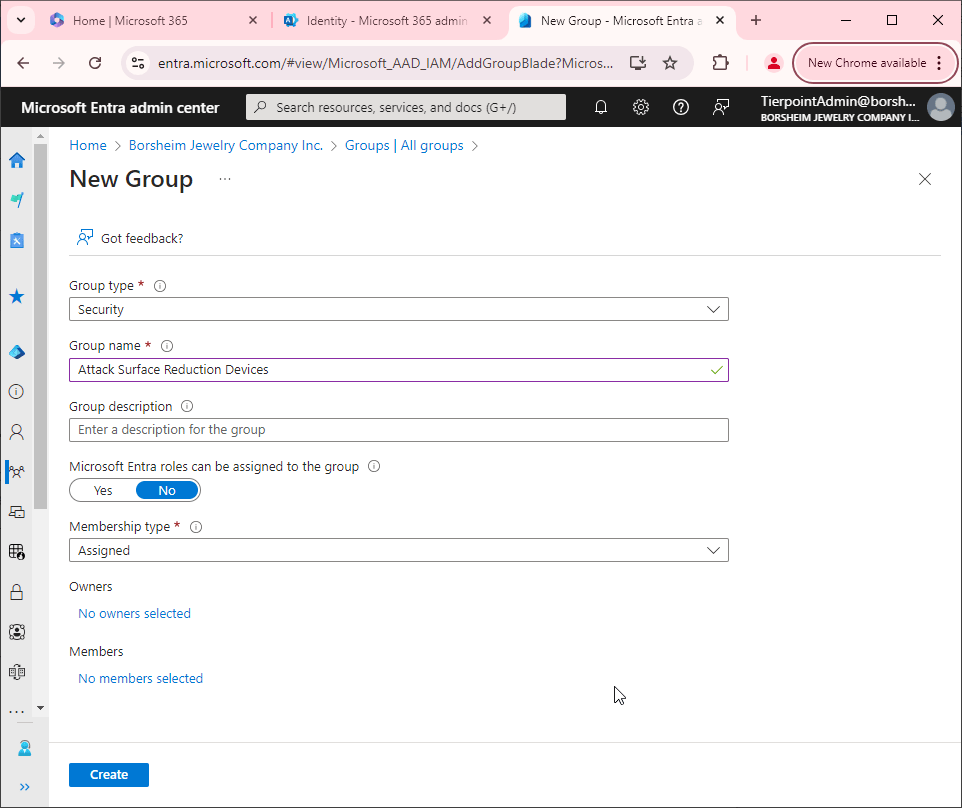
How to create a group to use in Microsoft Intune
How to create a group that can be used in Microsoft Intune.
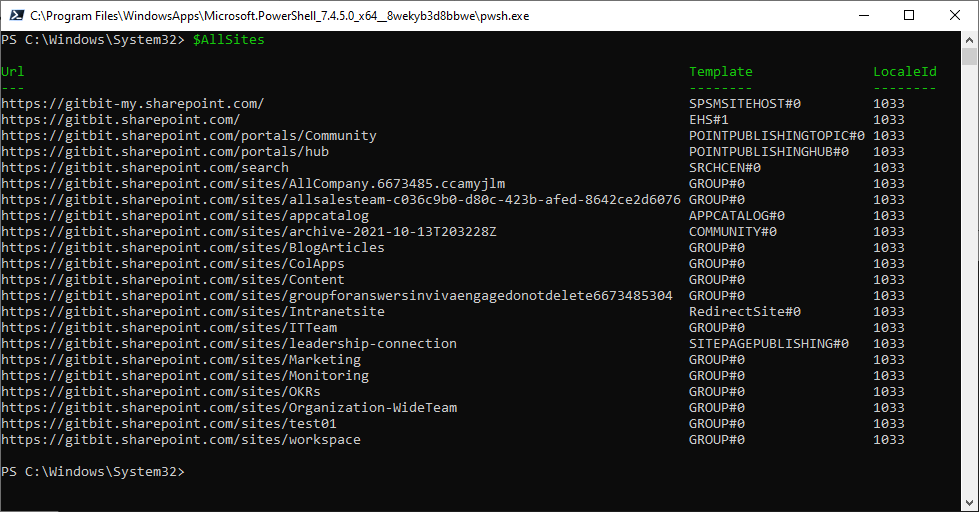
Get all SharePoint Sites including Subsites
Getting all the SharePoint subsites isn't easy. Fortunately, there's PowerShell, but it's not that simple.